Transforming Healthcare Through Innovation
Rural Health Transformation Program (RHTP)
We address all five RHTP strategic goals, eight statutory
requirements and support multiple qualifying uses of funds.
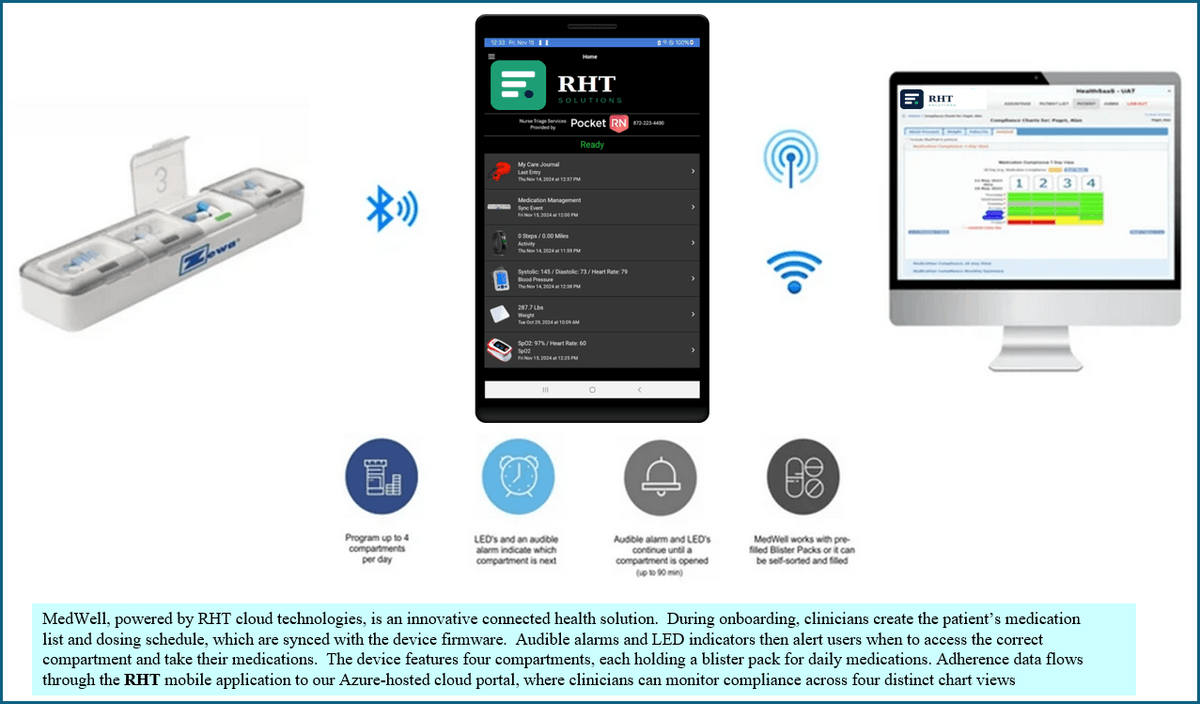
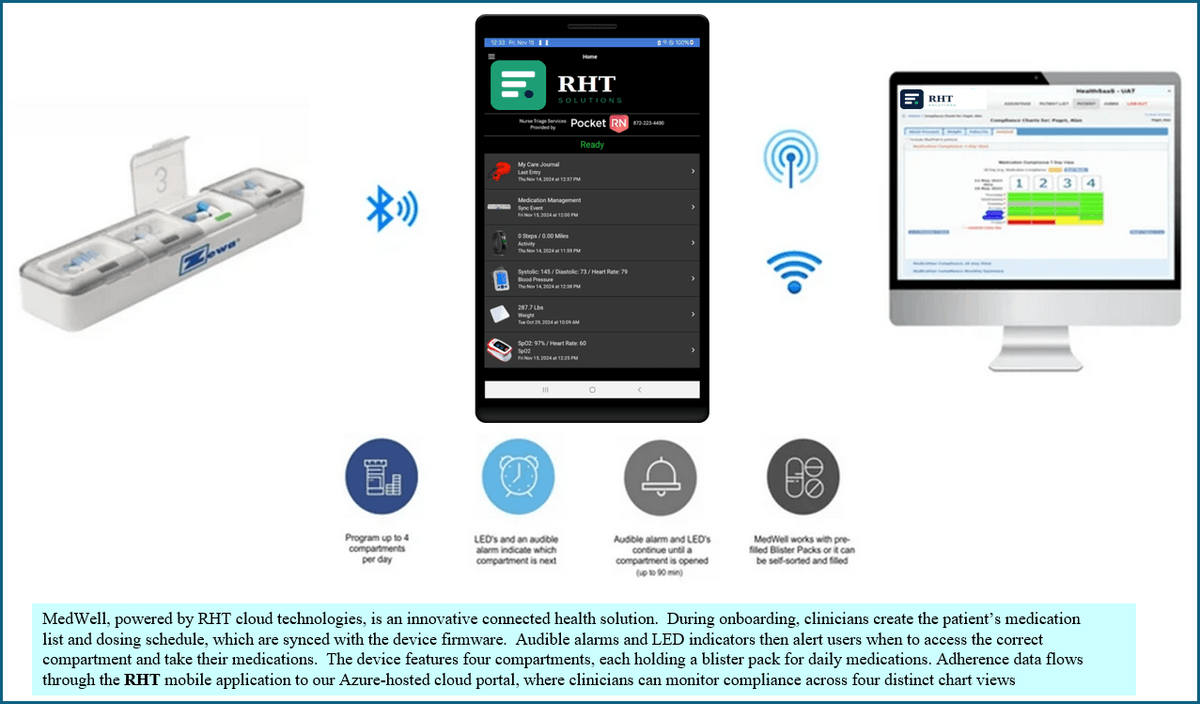
Medication Adherance - CCM/RPM
The right medication at the right time shouldn't be left to chance;
it should be driven by intelligent technology and expert care.
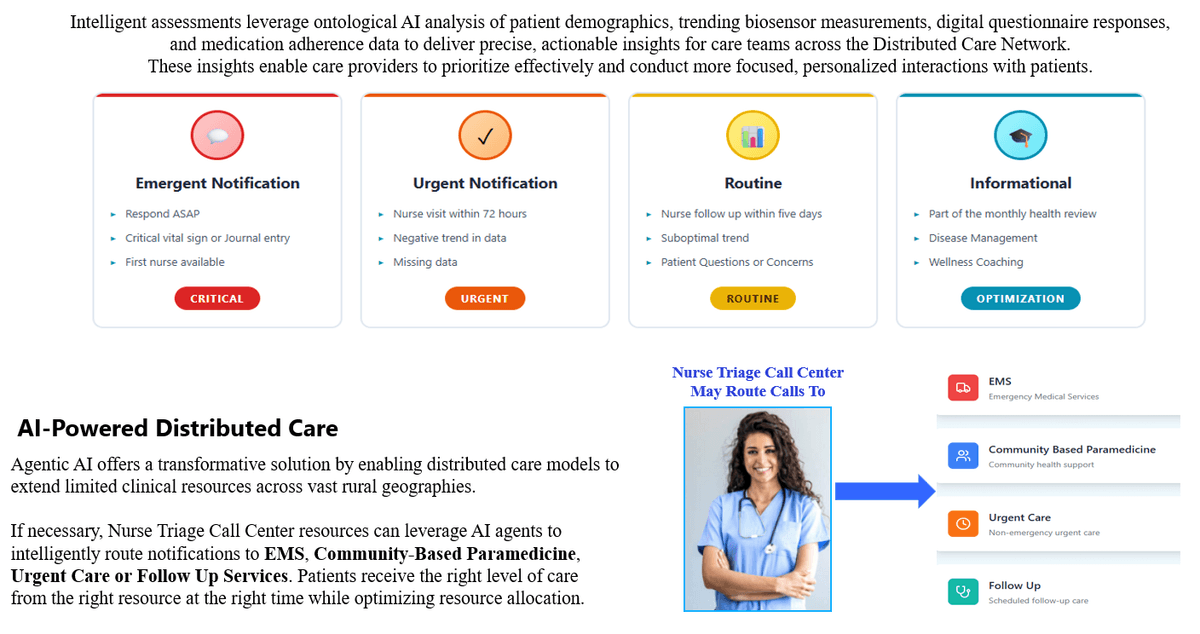
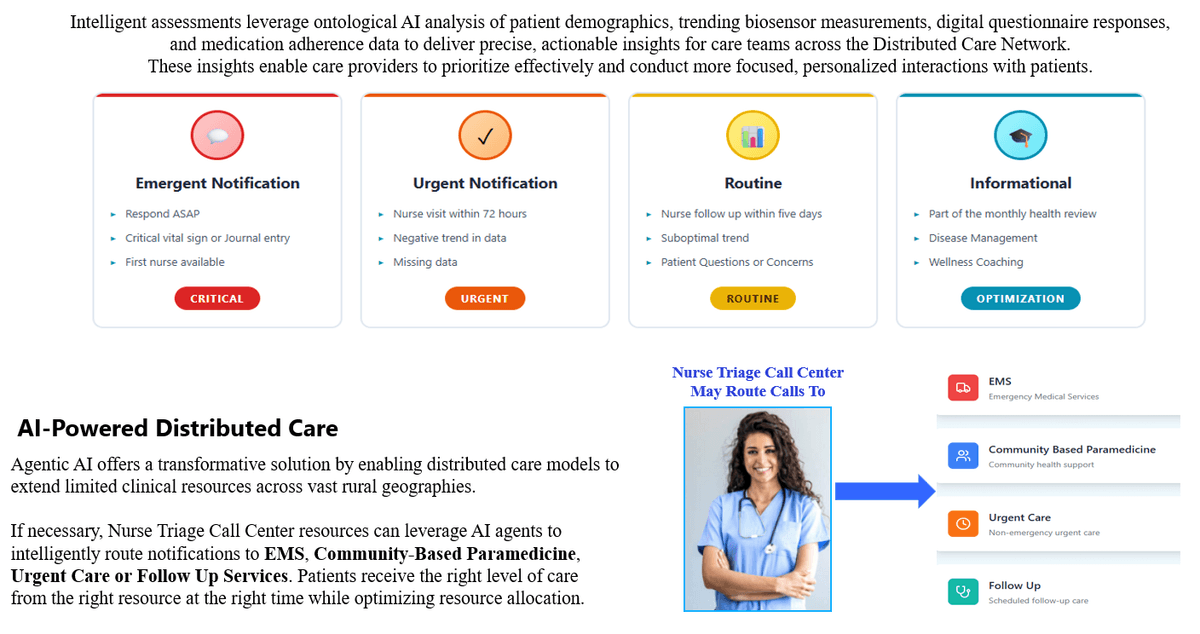
Distributed Care Triage
Security
Security is at the core of the RHT platform. From our Azure powered, private labeled portals, to private APIs, every access method is
safeguarded with authentication and encryption. All data transmission occursover SSL (HTTPS), which encrypts all transmitted data.RHT Solutions meets or exceeds all Health Information Technology for Economic and Clinical Health (HITECH) Act and HIPAA guidelines and
requirements.This applies to data security, integrity, and protection, as well as to data that is shared or transmitted from the HealthSaaS platform to any other
system.Our Business Associate Agreement (BAA) with Microsoft offers numerous services built to support healthcare compliance.
Key security measures include:Azure Health Data Services: A suite of managed services purpose-built forprotected health information (PHI), supporting open standards like FHIR® (Fast Healthcare Interoperability Resources) and DICOM® (Digital Imaging and Communications in Medicine) for data unification and secure exchange.
Compliance Certifications: Azure is HITRUST CSF certified and aligns with standards such as NIST SP 800-53, FedRAMP High, ISO/IEC 27001, and SOC 2.
Data Encryption: PHI is protected with encryption both at rest and in transit. Features like Azure Key Vault are used to manage encryption keys
securely.Identity and Access Management: Robust controls, including Role-Based Access Controls (RBAC), ensure only authorized personnel can access sensitive data.
Network Security: Azure offers built-in security features such as Azure Firewall, Web Application Firewall (WAF), and Network Security Groups to limit attack surfaces and protect against threats like DDoS attacks.
Threat Protection and Monitoring: Tools for monitoring activity logs, detecting suspicious activity, and receiving security advisories help organizations quickly identify and respond to potential threats.
AI and Analytics in a Secure Boundary: Healthcare organizations can leverage AI and machine learning tools, such as Azure OpenAI Service, within
the compliance boundaries established by the BAA, ensuring that PHI used for insights remains protected
Microsoft Azure Cloud Portals
Microsoft cloud services are built on a foundation of trustand security. Microsoft enables the best-in-breed security controls, monitoring, and protection to ensure that when you come to the cloud, it’s trustworthy. Microsoft uses the best development and operation practices outlined in Microsoft Security Development Lifecycle (SDL) and Microsoft Operational Security Assurance (OSA).Microsoft developers are required to validate that source code, documentation, configurations, and dependencies don’t cause unintended side
effects.